Circular Dependencies And Glue Records
Name servers in delegations are identified by name, rather than by IP address. This means that a resolving name server must issue another DNS request to find out the IP address of the server to which it has been referred. If the name given in the delegation is a subdomain of the domain for which the delegation is being provided, there is a circular dependency.
In this case, the name server providing the delegation must also provide one or more IP addresses for the authoritative name server mentioned in the delegation. This information is called glue. The delegating name server provides this glue in the form of records in the additional section of the DNS response, and provides the delegation in the of the response. A glue record is a combination of the name server and IP address.
For example, if the for example.org is ns1.example.org, a computer trying to resolve www.example.org first resolves ns1.example.org. As ns1 is contained in example.org, this requires resolving example.org first, which presents a circular dependency. To break the dependency, the name server for the top level domain org includes glue along with the delegation for example.org. The glue records are address records that provide IP addresses for ns1.example.org. The resolver uses one or more of these IP addresses to query one of the domain’s authoritative servers, which allows it to complete the DNS query.
Detecting Security Threats With A Proactive Approach
There has been significant research into using DNS analytics to detect fast fluxing and DGAs published in the years since IBM security researcher Douglas L. Schales socialized the concept in a report titled Stream Computing for Large-Scale, Multi-Channel Cyber Threat Analytics: Architecture, Implementation, Deployment, and Lessons Learned. With the above categories in mind and access to large data streams of ongoing DNS queries, domain name registration data and digital certificate registration information, what types of analysis can we perform to identify security threats?
Ahead-of-threat detection is an advanced approach to protecting users from malicious domains. Generally, malicious domain protection involves a time-of-use approach in a browser. Ahead-of-threat detection is a fundamentally different approach to finding potentially malicious domains, and the bad actors behind those domains, before an actual security threat is visible.
Threat actors typically generate malicious domains by applying generation methods, e.g., domain squatting. Ahead-of-threat detection finds those newly registered malicious domains from Quad9 and identifies the actors behind the domains. Additional analytics on related data WHOIS analytics and site image comparison, for example can reduce the chance of a false positive.
Dns: The Magic That Translates Website Names Into Ip Addresses
Every time you visit a website, you are interacting with the largest distributed database in the world. This massive database is collectively known as the DNS, or the Domain Name System. Without it, the Internet as we know it would be unable to function. The work that the DNS does happens so seamlessly and instantaneously that you are usually completely unaware that its even happening. The only time that youll get an inkling about what the DNS is doing is when youre presented with an error after trying to visit a website. Learn more about what the DNS is, how it works and why its so critical by reading on below.
Recommended Reading: What To Do After You Purchase A Domain Name
Why Are Dns Analytics Important
DNS is a critical component of the internet. It is essentially a telephone book that translates domain names into IP addresses. Because of its ubiquity, DNS provides a highly attractive channel for advanced threat actors to exploit the DNS system for a variety of threat vectors.
The image below shows the different ways actors misuse DNS in attacks, grouped by the stages of the Gartner Cyber Kill Chain. For example, a domain name that looks similar to a well-known domain can be easily overlooked by a user in a phishing email, or attackers may register domain names expecting victims to mistype their destination, a tactic known as typosquatting.
The DNS protocol is also one of the few application protocols that are allowed to cross network perimeters of organizations. As such, DNS provides a channel for threat actors and botnet operators to establish hard-to-block and stealthy communication channels between infected devices and command-and-control infrastructures. These include fast fluxing, domain generation algorithms and combinations thereof, as well as using the DNS protocol to exfiltrate secret information with covert tunneling techniques.
What Does It Mean To Own A Domain Name
Although people often speak of buying and owning domain names, the truth is that registries own all of their domain names and registrars simply offer customers the opportunity to reserve those domain names for a limited amount of time.
The maximum reservation period for a domain name is ten years. A user can hold onto a domain name for longer than ten years, as registrars usually let them keep renewing their reservation indefinitely. But the user never truly owns the domain they just lease it.
Read Also: How Do I Connect My Domain To Shopify
Configuration Of Dns Records
The domain registrar provides you with an interface to change/update name servers. There is a minimum of two nameserver records that need to be entered, usually NS1 and NS2.
Your web server will provide you with the Nameserver values which you need to enter here. This will automatically direct all the other web services to the mentioned nameservers. To make changes to other DNS records you need to login to your hosting panel.
The other option is to specify specific DNS records for each of the web services. For example, if you just want the website to direct to a different server you need to update the A Record. Similarly, if you want the emails to use a different Mail Exchange Server you need to just update the MX Records.
When Does Dns Switch To Tcp
The next natural question is: when will DNS messages exceed 512 bytes? Actually, this happens quite often in todays environment. When DNS was first implemented, the only thing that would be so large that it exceeded the 512-byte limit was a zone transfer, in which one DNS server sends every single resource record in the zone to another machine, usually another DNS server.
In modern DNS systems though, we are increasingly seeing resource record sets that have a larger combined size. For example, Figure FAQ-5 illustrates querying for www.example.com may yield results such as this :
Or the same query might return the following TXT records, each providing a specific function such as spam detection or site verification as demonstrated in Figure FAQ-6:
If a zone is signed by DNSSEC, it will routinely return large responses due to the cryptographic keys and signatures as shown in Figure FAQ-7:
As more and more people adopt newer features such as IPv6, spam avoidance, and DNSSEC, DNS is more likely to switch to TCP due to the larger response size.
Don’t Miss: How To Transfer Godaddy Domain To Shopify
Dns As A Security Tool
DNS resolvers can also be configured to provide security solutions for their end users . Some DNS resolvers provide features such as , which can block sites known to distribute malware and , and botnet protection, which blocks communication with known botnets. Many of these secured DNS resolvers are free to use and a user can switch to one of these services by changing a single setting in their local router. has an emphasis on security.
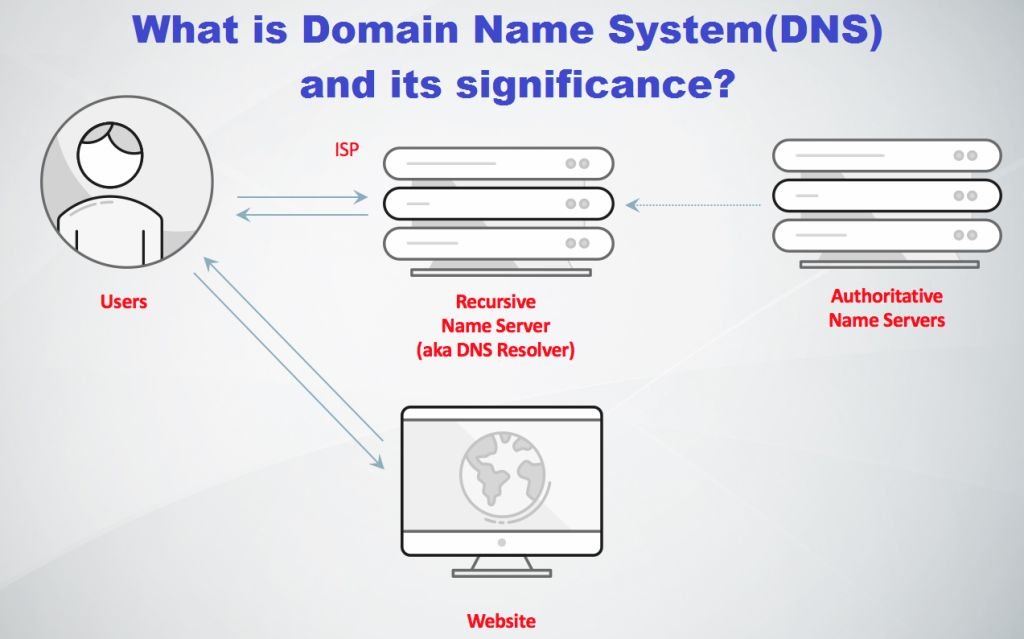
How Does A Dns Work
A DNS starts working immediately after a user enters a domain name in the address bar of a browser. It will search through the Internet to find the IP address that is associated with the entered domain name. After successfully identifying the IP address, it then guides the users browser to connect to it, which will then serve the requested website contents. The process happens very quickly with little delay and the user will be on his requested website almost immediately. However, in the background, a DNS has executed many processes.
The first step that a DNS does is to send a DNS query to several other DNS servers. A DNS is not just a single server responding to over billions of domain name requests, but instead it is distributed globally across a network of DNS, which stores the IP address directory in a distributed manner.
With this in mind, all the DNS servers work together to attend to the billions of domain names requests worldwide. The reason behind this is to cut down the time for users to get a response for their requests. If a user is looking for a specific site and there is only one DNS server to process it, then it will take significantly longer to search through the millions of records in the directory. What if at the same time there are also millions, if not billions of users who are also doing the same? That is going to take a long time, and the users browsing experience will definitely be affected negatively.
Don’t Miss: How To Change Your Wix Domain Name
What Is A Dns
Every website on the Internet has its own unique address. Its called an IP address. But unlike the physical street address for a house or building, an IP address consists of a set of numbers strung together and separated by periods. A typical IP address in the IPv4 address space looks like: 123.123.123.2. If customers had to memorize the IP addresses of every website they visited, they wouldnt spend much time on the Internet. Thankfully, we use URLs instead. And behind the scenes, theres an address book of sorts that helps convert these user-friendly URLs and web addresses into the IP addresses that computers understand. Its called a Domain Name System, or DNS.
In the simplest form, a DNS is a directory of domain names that align with IP addresses. They bridge the gap between computer language and human language keeping both servers and people happy.
How To Use Dns Analytics To Find The Compromised Domain In A Billion Dns Queries
Finding a needle in a haystack is hard, but its nothing compared to finding a single piece of hay in the haystack that was put there with malicious intentions.
As Verisign noted in its August 2018 Domain Name Industry Brief, there were around 339.8 million registered domains at the end of the second quarter, with approximately 7.9 million new domains registered in the last year. Additionally, public Domain Name System providers log hundreds of billions of queries every day. Cloudflare reported that it serves 130 billion DNS queries per day, and in 2014, reported that it served more than 400 billion DNS queries per day. Furthermore, Lets Encrypt issues around 600,000 digital certificates per day.
Buried in all this information are clues to past compromise, ongoing attacks and future malware campaigns. The goal of advanced DNS analytics is to transform this data into actionable threat intelligence, which enables security teams to block domain names, detect infected devices, identify insider threats and assess an organizations overall security hygiene.
You May Like: How To Transfer Google Domain To Squarespace
What Happens If Tcp Is Blocked
Whatever the case, when the message size exceeds 512 bytes, it will trigger the TC bit in DNS to be set, informing the client that the message length has exceeded the allowed size. In these situations, the client needs to re-transmit over TCP, which has no size limit. If DNS servers and network environment cannot support large UDP packets, it will cause retransmission over TCP if TCP is blocked, the large UDP response will either result in IP fragmentation or be dropped completely. The end symptom to the end client is usually slow DNS resolution, or inability to resolve certain domain names at all.
What Is Dns And How Does It Work
The Domain Name System is a system used to convert a name into an IP address . These addresses are used by computers to communicate with each other on the internet. Most people find remembering names much easier than numbers, so DNS makes this process easy.
When you visit a website, your computer, phone or tablet will first check your local DNS cache for the corresponding IP address. If your device has not recently looked up this website, then it will need to ask your configured DNS server which will forward the request on to the DNS server responsible for managing the records. This process is known as a DNS lookup request.
Once the IP address is known, it is stored locally for a set period of time known as the Time To Live and used to speed up future requests. Updated records will not be returned until this time has expired, this can often be the cause of why DNS changes do not appear to be working right away.
Don’t Miss: How To Get Free Tk Domain
What Is A Domain Name Server
A DNS is a computer server that contains a database of many IP addresses and their associated domain names. It serves to translate a requested domain name into an IP address, so that the computer knows which IP address to connect to for the requested contents. The Internet is a network of connected computers, and they communicate with each other through IP addresses. A DNS plays an important role in helping us to conveniently use the Internet and it is one of the most essential foundations of the Internet as we know it today.
It is much easier for us to remember a domain name, webnic.cc, rather than a string of numbers, 104.20.73.209 to WebNICs website. Both the domain name and the DNS are extremely important and they work together to make this possible. Read our blog here if you are unsure what is a domain name.
A great example is to see a DNS as a phone book, which matches a name to a telephone number. You can search for the name you want and find the corresponding phone number. It is also a similar concept to your smartphones contact list, which will match a contact name to a phone number. Remembering domain names is definitely easier for us than to remember a string of numbers. DNS helps us to do this by match domain names to IP addresses, and simplifies our web surfing experience significantly.
What Is Domain Name System
Domain Name System is a hierarchical naming system built on a distributed database for computers, services, or any resource connected to the Internet or a private network. Most importantly, it translates human readable domain names into the numerical identifiers associated with networking equipment, enabling devices to be located and connected worldwide. Analogous to a network phone book, DNS is how a browser can translate a domain name to the actual IP address of the server, which stores the information requested by the browser.
DNS Basics
The domain name system is responsible for translating domain names into a specific IP address so that the initiating client can load the requested Internet resources. The domain name system works much like a phone book where users can search for a requested person and retrieve their phone number. DNS servers translate requests for specific domains into IP addresses, controlling which server users with access when they enter the domain name into their browser.
A Brief History of DNS
As the Internet grew to millions of domains, this was not sustainable. In 1983, Paul Mockapetris, a USC researcher, was tasked with developing a solution. His solution was a new system that he named DNS, which remains based on Mockapetris fundamental principles. Today, the standards for DNS are maintained by the Internet Engineering Task Force in RFC 1035.
How DNS Servers Work
DNS servers and IP addresses
The DNS Lookup Process
Types of DNS Services
Read Also: How To Buy My Domain Name