Additional Terms To Know
Heres some critical information to understand:
- An identity can be a single user or computer. It can also be a group of users or computers. When you look at Active Directory Users and Computers , you see user names and security group names. These are identities.
- A security principal is used to authenticate an identity and is what handles what permissions an identity has. Its used to prove that an identity is genuine.
- A security identifier is just a key that is associated with an identity that determines authority on the domain.
- An account is either a user or computer. A user account stores information related to the user identity and is used to verify access to network resources such as file shares.
A computer account contains information that authenticates the account to the domain. Every computer account includes a unique security identifier .
What Is The Role Of Active Directory
Since Active Directory is mentioned a lot, and I will keep mentioning it, its time to explain what it is. Essentially, its the central database that stores everything about a company. I dont mean that it stores files and images, but it stores the users, clients, and servers.
Lets put this in a story for easier understanding. Take, Sara. She starts a new job at Company A. If Sara is ever going to be able to login to the computers, she needs to have an active account in Active Directory. This is because when Sara tries to log in to a computer, the computer will check with Active Directory to see if Sara exist as a user and if she is permitted to log in to the computer.
When Sara has logged in, she needs to print out some documents. Because she is part of Active Directory, as well as the computer she is on, she can easily reach a shared network drive where the document is. Because Active Directory also has sent out some default settings for her, she already has the office printer installed and set as default printer, making it easier for Sara to print out the document.
Active Directory holds all the users, computers and servers. But its important to note that what holds everything together is a domain, not Active Directory. The AD should be seen as a database that holds information while a domain is what makes everything talk to each other.
What Is The Use Of A Read
A Domain controller can also be Read-Only, called RODC . An RODC is a domain controller that cant write to Active Directory. It is still being synced from other domain controllers to get the latest information, but it cant update itself. This is often useful if you need an application to read from Active Directory for example.
If the application would go bad, or if someone is trying to find a weakness in the application, they get to a domain controller that can only be read. Its bad but they cant make it worse by entering the wrong information to the database, which is good .
It can also be used on other offices where just authentication is needed. When a user login to a computer, the computer doesnt need to write anything to the domain controller, just check that its OK for the user to login = read.
Don’t Miss: Where To Buy Co Domains
Why Domain Controllers Are An Important Part Of Active Directory
Domain controllers provide the physical storage for the AD DS database. In addition, they also provide services that allow enterprises and IT pros to manage their servers, computers, laptops, users, printers, and other applications. They are vitally important to your network and need to be secured. A malicious user, if they can take control of a DC, could wreak havoc on your Friday afternoon by wiping out your AD database.
What Is A Domain Controller When Is It Needed + Set Up
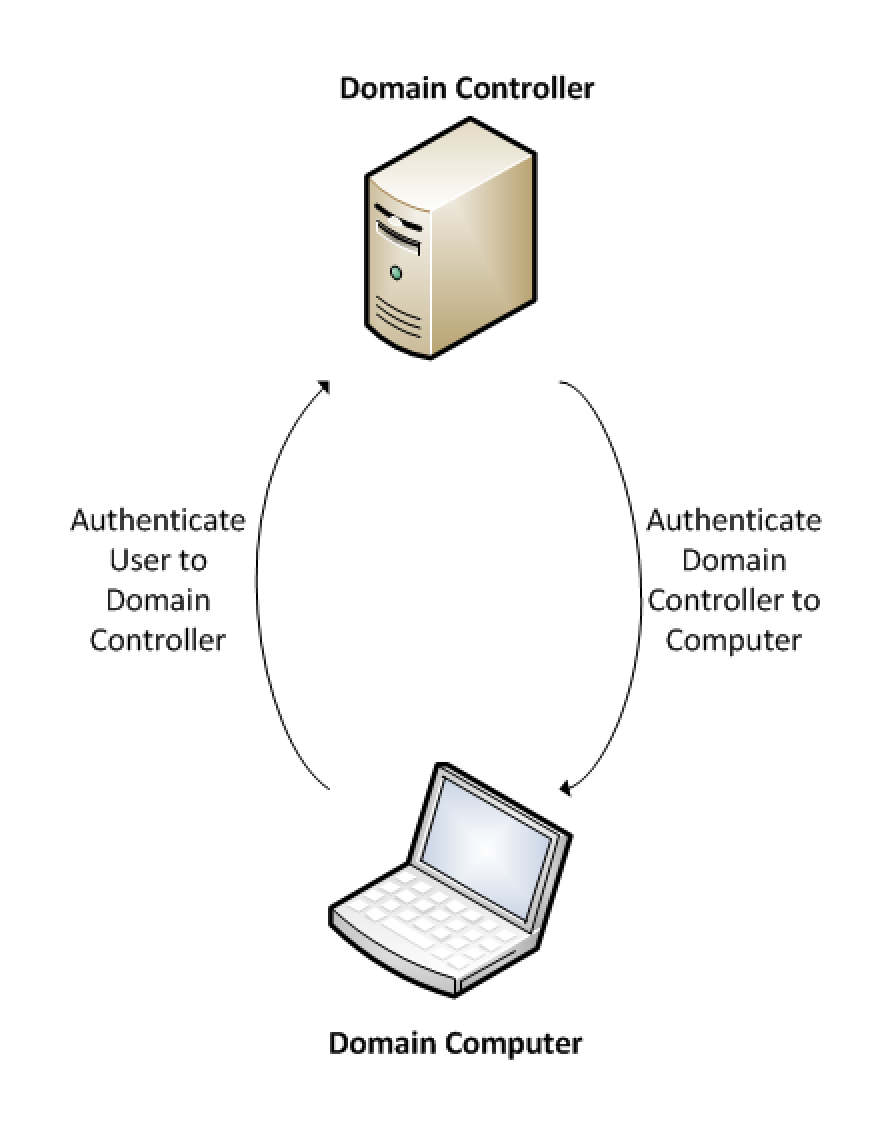
A domain controller is a server that responds to authentication requests and verifies users on computer networks. Domains are a hierarchical way of organizing users and computers that work together on the same network. The domain controller keeps all of that data organized and secured.
The domain controller is the box that holds the keys to the kingdom- Active Directory . While attackers have all sorts of tricks to gain elevated access on networks, including attacking the DC itself, you can not only protect your DCs from attackers but actually use DCs to detect cyberattacks in progress.
Read Also: How To Lookup Who Owns A Domain Name
Install Ad Ds On Azure Vms
Sign in to a VM and verify that you have connectivity across the site-to-site VPN or ExpressRoute connection to resources on your on-premises network. Then install AD DS on the Azure VMs. You can use same process that you use to install an additional DC on your on-premises network . As you install AD DS, make sure you specify the new volume for the location of the AD database, logs and SYSVOL. If you need a refresher on AD DS installation, see Install Active Directory Domain Services or Install a Replica Windows Server 2012 Domain Controller in an Existing Domain .
Definition And What Does A Domain Controller Do
I am using the computer for ages and will tell you about what does a domain controller do, and what actually it is.
Definition-
A domain controller is a server that responds to security authentication requests within a Windows Server domain. OR
A domain controller is a server that manages network security, effectively acting as the gatekeeper for user authentication and authorization. Domain controllers are particularly relevant in Microsoft directory services terminology, and function as the primary mode for authenticating Windows user identities.
These are the functions of the domain controller
Domain controllers host and replicate the directory service database inside the forest. The directory service also provides services for managing and authenticating resources in the forest. These servers host essential services in AD DS, including the following:
1) Kerberos Key Distribution Center
2) NetLogon
Also Check: How Much Does It Cost To Have Your Own Domain
Control The Security Settings Of Your Company Files And Programs
Another significant benefit of a domain controller is monitoring who has access to what kind of data in your organization. By knowing who has access to what, youre able to maintain a close eye on possible irregularities.
I can go ahead and secure my infrastructure, lock things down, Schenk said.
The domain controller also gives you the advantage of seeing who is trying to access your network but is failing this lets your IT team know they should watch that users behavior.
How To Enable/disable The Global Catalog Role On A Domain Controller
You can enable the Global Catalog role on a domain controller in several ways:
- Using the graphical Active Directory Sites and Services mmc console
- Using PowerShell
- Using the dsmod.exe tool.
Run the mmc snap-in Active Directory Sites and Services .
Expand the Sites section and find the AD site that contains your domain controller. Expand it, right-click on NTDS Settings and then select Properties.
Set the Global Catalog checkbox on the General tab to enable the GC role, or uncheck it to disable it. Click OK to save your changes.
Once promoted to a GC server, an event with Event ID 1110 should appear in the Directory Service section of Event Viewer:
Event Source: NTDS General
After successful installation of the role, Event ID 1119 will appear:
This domain controller is now a global catalog
In this case, the value of the Global Catalog Promotion Complete registry setting under the HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters key registry should be 1.
You can make a read-only domain controller a Global Catalog server. A Global Catalog server is a read-only copy of a partial set of attributes of all domains in an AD forest, so you can use this role on a Read-Only Domain Controller . But some applications will not work correctly with a GC server running on an RODC. Thats why its important to make sure your apps support a GC server running on an RODC.
You can enable the Global Catalog role on a DC using the PowerShell command:
Don’t Miss: How To Get A Web Domain Name
Azure Has The Solution
If your business currently runs on a single Domain Controller setup, adding a secondary Domain Controller is made easy thanks to Azure. In a short amount of time, your business can have a secondary DC setup and ready-to-go, contained within the Azure cloud.
With a newly implemented solution, your company can enjoy resilience in your Active Directory environment, giving your business peace of mind.
Plus, the best part is that this approach actually comes with multiple benefits for your business. In addition to keeping your servers up and running, your business will also gain an identity platform in the cloud with this setup.
Once you have extended your Active Directory to the cloud, it will be easy for your company to begin deploying new applications into Azure instead of on-premises.
Additionally, more and more companies are seeking these updates in an attempt to become GDPR and Cyber Essentials compliant. In fact, there are countless reasons why your business should take action and take the next steps
How Many Domain Controllers Do You Need
In their original Windows implementation, domain controllers were divided into two categories: primary domain controller and backup domain controller . A primary DC is the first-line domain controller that handles user-authentication requests. Only one primary DC can be designated. According to security and reliability best practices, the server housing the primary DC should be solely dedicated to domain services. Because of its central importance to the network, the primary DC server must not run file, application, or print services, which could slow it down or risk crashing it.
A backup domain controller exists as a fail-safe in case the primary domain controller goes down. There can be multiple backup domain controllers for redundancy. Having a dedicated backup DC is a wise precaution. If the primary DC fails and theres no backup, users will not be able to gain access to the network. When a user attempts to log in, the software contacts the primary DC. If the primary DC is unavailable, it then contacts the backup DC. The backup can be promoted to the primary role in the event that the primary is permanently out of service. Note that domain updates can only be made to the primary DC. They are then propagated into the backup DC databases. This is a form of the master-slave replication structure, with the primary DC being the master and secondary DCs being the slaves.
For more information on domain controllers and Active Directory, read through our related blog articles.
Recommended Reading: How To Purchase An Email Domain
Create An Azure Virtual Network
In the Azure classic portal, click New> Network Services> Virtual Network> Custom Create and use the following values to complete the wizard.
| On this wizard page | |
|---|---|
|
Name: Type a name for the virtual network, such as WestUSVNet. Region: Choose the closest region. |
|
| DNS and VPN connectivity |
DNS Servers: Specify the name and IP address of one or more on-premises DNS servers. Connectivity: Select Configure a site-to-site VPN. Local network: Specify a new local network. If you are using ExpressRoute instead of a VPN, see Configure an ExpressRoute Connection through an Exchange Provider. |
| Site-to-site connectivity |
Name: Type a name for the on-premises network. VPN Device IP address: Specify the public IP address of the device that will connect to the virtual network. The VPN device cannot be located behind a NAT. Address: Specify the address ranges for your on-premises network . |
| Virtual network address spaces |
Address Space: Specify the IP address range for VMs that you want to run in the Azure virtual network . This address range cannot overlap with the address ranges of the on-premises network. Subnets: Specify a name and address for a subnet for the application servers and for the DCs . Click add gateway subnet. |
Next, youll configure the virtual network gateway to create a secure site-to-site VPN connection. See Configure a Virtual Network Gateway for the instructions.
Why Your Business Should Be Using A Domain Controller To Boost Data Security And Lower Costs
by AJ Gyomber | Sep 4, 2018 | Security
When a company is just starting out, there may be only a handful of employees and computers to keep up with. But as both numbers grow to 10, 25, 50+ staff and computers on your network, keeping your technology secure and centrally controlled becomes a challenge.
What happens if you add sensitive payroll files on your cloud storage network and want to restrict access? Do you need to have someone go to each computer individually to set that up? Not if youre using a domain controller.
Domain controllers might seem like a foreign concept to some companies, but its really a simple idea. They allow you to control and set security and access parameters for any device connected to your network, all from one single location. They have a few other benefits too, that well discuss.
As innovators in business technology, Technology Visionaries seeks out the best applications and software to help companies work faster, securely, and more efficiently. Domain controllers are one of those best kept secrets that we bring to our clients.
Unsecure devices cause data breaches that cost businesses big time.
Data breaches cost companies on average $148 per each lost or stolen record that contains sensitive information. If 100 client files are stolen due to an unsecure computer on your network, thats nearly $15,000 in costs.
Don’t Miss: Is Com The Best Domain
How To Determine Your Pc Domain Controller
If you use Windows Server Systems in your small business, one of your computers acts as a domain controller . However, it can be difficult to know which computer is the domain controller, especially if someone else configured your network. Because the domain controller responds to all security authentication requests, including logging in, all you have to do to determine your PC domain controller is find the computer that validates the user account when you logged in.
1.
2.
How Are Domain Controllers Set Up In Active Directory
Domain control is a function of Microsoft’s Active Directory, and domain controllers are servers that can use Active Directory to respond to authentication requests.
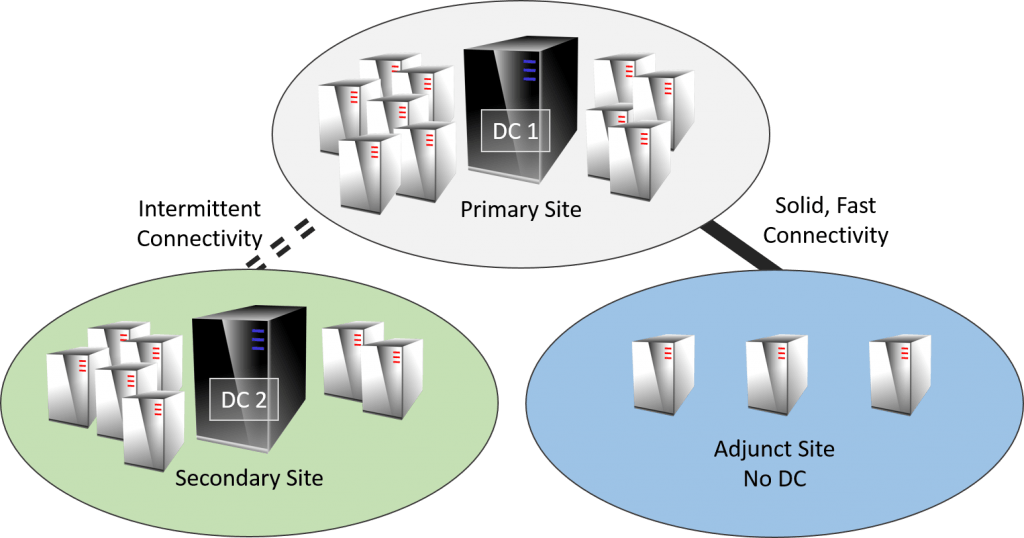
Experts advise against relying on a single domain controller, even for smaller organizations. Best practices call for one primary domain controller and at least one backup domain controller to avoid downtime from system unavailability.
Another best practice is to deploy each domain controller on a standalone physical server. This includes virtual domain controllers, which should be run on virtual machines running on different physical hosts.
Domain controllers can be deployed on physical servers, running as VMsor as part of a cloud directory service.
Steps for setting up an AD domain controller include:
Specifics for setting up and configuring AD domain controllers vary depending on the version of Windows Server in use on the domain.
See video below for how to set up a domain controller in Windows Server 2019.
You May Like: How To Create Sub Domain
So Can Azure Ad Fully Replace The On
The short answer is no. Not yet anyway. Azure AD is not actually a cloud replica of the original.
Replace is the key here â it is possible to replace on-premises AD with Azure AD as long as you donât have legacy applications that require a local domain controller. Itâs also possible to replace some Group Policy functionality with Microsoft InTune. In many cases, when a company goes through a divestment , the new environments can be Azure AD only as they can setup as greenfield and donât need to bring forward the on-premise infrastructure. There are also scenarios where itâs desirable to move away from on-premise infrastructure and Microsoft 365 and Azure AD allow you to do that.
Until you can go 100% cloud, your best bet is to use the two solutions together to handle access-management for both cloud and on-premise applications.
Recommended Reading: How To Find Out Who Owns Domains
Troubleshooting The Domain Locator Process
To troubleshoot the domain locator process:
Check Event Viewer on both the client and the server. The event logs may contain error messages indicating that there’s a problem. To view Event Viewer, select Start, point to Programs> Administrative Tools, and then select Event Viewer. Check the System log on both the client and the server. Also check the Directory Service logs on the server and DNS logs on the DNS server.
Check the IP configuration by using the ipconfig /all command at a command prompt.
Use the Ping utility to verify network connectivity and name resolution. Ping both the IP address and the server name. You may also want to ping the domain name.
Use the Netdiag tool to determine whether networking components are working correctly. To send detailed output to a text file, use the following command:
netdiag /v > test.txtReview the log file, looking for problems, and investigate any implicated components. This file also contains other network configuration details.
To fix minor problems, use the Netdiag tool with the following syntax:
netdiag /fix.
Use the nltest /dsgetdc:domainname command to verify that a domain controller can be located for a specific domain.
If either of these commands doesn’t succeed, use one of the following methods to reregister records with DNS:
You May Like: What Are Three Security Domains
What Are The Main Functions Of A Domain Controller
Domain controllers restrict access to domain resources by authenticating user identity through login credentials, and by preventing unauthorized access to those resources.
Domain controllers apply security policies to requests for access to domain resources. For example, in a Windows AD domain, the domain controller draws authentication information for user accounts from AD.
A domain controller can operate as a single system, but they are usually implemented in clusters for improved reliability and availability. For domain controllers running under Windows AD, each cluster comprises a primary domain controller and one or more backup domain controllers . In Unix and Linux environments replica domain controllers copy authentication databases from the primary domain controller.